Switching System 7 (SS7) Security flaws
A serious flaw in the Global Cellular System
© 2016 - by John T. Draper
Over the last 15 years, I have been traveling back and forth regularly to Germany to give talks at various conferences. Many of the connections I’ve made over this time have had something to do with computer security.
In the last few years, the big subject on everyone’s lips is the overlooked vulnerability of SS7 (Signaling System 7).
For those who have no idea what SS7 is… it’s basically a set of signalling protocols used by Telecommunication Companies, to communicate information over a dedicated channel. A dedicated channel being outside the ‘normal’ channel used for voice or data. SS7 is not communicated between phones, but between mobile networks.
The SS7 network replaced the older ‘in-band’ system, but of course was not designed to be used by the newer Cellular technology like SMS, caller ID, and other cell phone features.
So this outdated 40-year-old system is still being used by almost every phone in the world when connecting to a long distance network, including when sending SMS messages.
It was originally a closed system, used only by the ‘Telcos’ (Telecommunication Companies) within their internal network. In the early 90’s, it became necessary to open up SS7 to 3rd party developers and cellular phone companies, and since then there have been increasing concerns over its flaws. Although it will be a long process, there is no doubt that it should be upgraded to meet the security demands of any participating Telcos in the future. I believe that what we need are SS7 Firewalls at each Telco.
Why am I involved in advocating for this upgrade? Well, as many of you will probably know, I was one of the first to literally ‘blow the whistle’ on AT&T’s bright idea of passing the signalling information to the distant switch, by using nothing more than a toy whistle found in Cap’n Crunch cereal.
I was also involved in building Blue Boxes - a device which emitted specific preset tones emulating the phone company’s internal signalling equipment, where one could easily pass commands from one exchange to another. A Blue Box was easy to make. Any hobbyist knowledgeable in electronics could build one. The specific frequencies were even published in the Bell System Technical Journal, found in most College Libraries.
That was back when the Telcos were in the decade-long process of gradually switching over from SS6. When it was complete, in 1975, AT&T ‘long lines’ began deploying the first ‘out of band’ link using what was then called (CC)SS7 or CCIS (Common Channel Interoffice Signalling). This got rid of the Grand Canyon sized hole, but left many other unscrupulous activities possible, especially with increasing mobile phone users 15 years later.
In the early 90s, with the growing popularity of cellular phones, more and more third party Telcos were using SS7 protocols. In developing countries like India, building up the mobile infrastructure was a lot easier than trying to fix the country’s outdated hard wired system, but connecting to the SS7 network was still essential. Thus the decision to interface SS7 to the Internet via SIGTRAN (basically SS7 with Internet Protocols added) was the only way to go.
Now to the present day. We have record numbers of cellular users worldwide, all connected through a system with huge vulnerabilities, written 40 years ago. It’s staggering.
What about Signal and WhatsApp you say? Well guess what, if an attacker knows your phone number, they can hijack your Signal or WhatsApp application by sending a forged SMS message. They just hack the SMS messages through SS7, and snatch away the target’s Signal account. The only way you would know about it is when you no longer get any Signal calls or text messages.
This also would work for WhatsApp, or any other mechanism that uses SMS for 2 factor authentications. The actual content of voice communication is encrypted however by using the Open Whisper Systems protocol (developed by Phil Zimmerman of PGP fame).
The SS7 vulnerability today is like the early 90’s pre-firewall era of the Internet… before programs like ISS (Internet Security System Inc) and SATAN (Security Administrator Tool for Analyzing Networks). Now the Telco’s are realizing that it’s important to see who’s knocking at the door instead of just letting everyone just walk in.
How the SS7 flaw has been already been used against you
A Washington Post article released in August of 2014 showed a long standing and cosy relationship between Law Enforcement and the Telcos. There have been numerous ‘closed’ trade shows in recent years, catering to the justice department, and pushing products like SkyLock. This system was built and designed for legal use by Law Enforcement, and the product description clearly defines its use of SS7 to extract info from any cell phone user, anywhere in the world,
Process this, and it becomes pretty clear why information on the SS7 flaw has been suppressed. The NSA wanted to keep it to themselves as much as possible. Everything that SkyLock can do is made possible by hacking into SS7 or using an IMSI catcher (cell tower impersonator).
But this is not new. Back in 2006, the Electronic Frontier Foundation (EFF) filed a class action lawsuit against AT&T, for violating the law and the privacy of its customers by collaborating with the National Security Agency (NSA) in a massive illegal program to wiretap and data-mine US citizens communications. Whistleblower Mike Klein reported that their ‘special equipment’ was located at the Folsom St. A.T.T. network office in San francisco, in the famous Room 641A.
What needs to change, and how we are still vulnerable
The more blatant holes in SS7 have been patched up, thanks to the work of SR Labs in Berlin. I’m told that all four German providers can now stop the ‘InsertSubscriberData’ SS7 command from entering at their ‘borders’. Unfortunately, this is not the only SS7 command used by hackers (and Law Enforcement).
Coupled with IMSI Catchers like Stingray, which is shrouded in secrecy, and known only to those who sign a strict NDA, its real capacity for privacy violations is totally unknown to ‘John Q Public’. The current laws regarding the use of IMSI Catchers is currently being argued by the lawmakers, and the FCC is looking into the illegal use of these devices, but I’m sure the AUP (Acceptable Use Policy) is chock full of legalese to protect the perpetrators of this questionable use of technology. A surveillance tool like SkyLock combined with IMSI Catchers like Stingray, provide maximum ‘droolage’ for Law Enforcement organizations, so don’t expect a good ruling anytime soon.
What can we do? Well, we can actively connect with the FCC, as Alan Grayson did. I have chosen to work on the problem in a more personal way. I watched presentations from the archived CCC (Chaos Computer Club) Congress sessions, then started sleuthing around the net, informing myself in detail on the SS7 network. In September this year, about a week or so before I flew to Berlin to host the second Geek Fest, I started reaching out to more people in Germany, including Benjamin from SecurityResearch in Germany. Below is a link to a portion of the GeekFest featuring Karsten Nohl, one of our Panelists.
I bookmarked a load of articles from the web, and read them on the long 12 hour flight to Berlin. I travelled days ahead of time, giving myself enough time to work with Benjamin, and also Oliver Soehlke, my Geek Fest ‘partner in crime’. Through Oliver I was able to locate Karsten Nohl, the security researcher, and authority on the SS7 flaw. We met just before the second day of the GeekFest, and Karsten agreed to be on the second panel. Prior to the event, I had a few hours with him to get any gory details of the SS7 flaws I didn’t know about. I also interviewed him for about 20 minutes, and posted the video to my YouTube.
As I write this article, there are a number of tools to help penetration testers find the SS7 flaws. Groups who have vested interests now have specialised teams working to help combat the problems. For instance The Internet Engineering Task Force (IETF), a working group involved in developing standards, have defined level 2, 3, and 4 protocols compatible with SS7 which use the Stream Control Transmission Protocol (SCTP) transport mechanism, the link between the internet and SS7. This suite of protocols is called SIGTRAN. There are also tools available for scanning and discovery of SIGTRAN servers, like the Network and Port Scanner by P1 Security. This scanning tool scans a range of IP addresses, looking for the ‘entry port’ into SS7, much like the scanners used to hunt down specific servers or computers on a network.
People using programs like Wickr Me, an encrypted text chat system that uses a chosen user-name and password instead of a phone number, can remain impervious to the flaw, but no matter what, the SS7 hacker can geo-track a target in real time, listen to their calls, and read their SMS messages, as well as gather a lot of other sensitive private information, just by knowing their phone number. Someone using Signal or WhatsApp, can take comfort in knowing that a hacker will not know who you’re talking to or what you’re saying, so at least this part can remain private.
I can assure you, that most Telcos are fully aware of this attack vector, and most are building up better defenses by deploying firewalls and filters. Since it is difficult to distinguish legitimate traffic, these flaws may remain in effect for a very long time as Telcos scramble to deal with it. The newer DIAMETER protocol might offer better security controls, but will no doubt have their own security issues. DIAMETER systems are being tested and deployed in the newer LTE Cellular networks, which offers faster data speeds than 4G.
Other relevant links:
Invasive phone tracking: New SS7 research blows the lid off mobile security
http://www.zdnet.com/article/invasive-phone-tracking-new-ss7-research-blows-the-lid-off-personal-security/
SS7 Vulnerability Isn’t a Flaw — It Was Designed That Way
https://securityintelligence.com/ss7-vulnerability-isnt-a-flaw-it-was-designed-that-way/
Map of the world, along with the Global Risk to privacy and Network exposure
http://ss7map.p1sec.com/
Australian news program 60 Minutes piece where this flaw was demonstrated
Locating Mobile Phones using Signalling System #7, by Tobias Engel
http://berlin.ccc.de/~tobias/25c3-locating-mobile-phones.pdf
The Carmen SanDiego Project.
https://media.blackhat.com/bh-us-10/whitepapers/Bailey_DePetrillo/BlackHat-USA-2010-Bailey-DePetrillo-The-Carmen-Sandiego-Project-wp.pdf
SS7 hack explained: what can you do about it?
https://www.theguardian.com/technology/2016/apr/19/ss7-hack-explained-mobile-phone-vulnerability-snooping-texts-calls
I hope you walk away after reading this article and conclude that although SS7 hacking is possible, and by no means trivial, it can be defended against to a degree, and hopefully prevented completely at some point in the future.
John T Draper AKA The Crunchman
jdcrunchman@gmail.com
Nice to see your 2nd post here :)
Small tip: you can set your avatar here: https://steemit.com/@jdcrunchman/settings
Yea, I know, plus the links didn't come out like I wanted it... :-) I'll try and fix it tomorrow. Its like 1:30 am here in Vegas.
Vegas, Baby! :)
for the links, if you're using markdown and not the raw HTML, use
[GitHub](http://github.com)which turns automatically into GitHubHow do I know I'm using this "markdown" feature?
It's the default choice when you're replying to comments or submitting a new post i think. You should be able to easily identify it as you see messages about it:
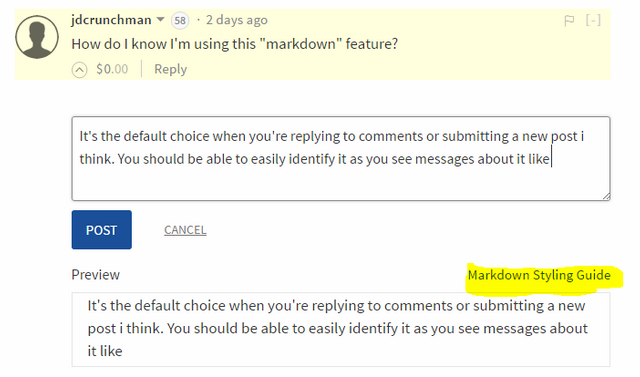
When writing a new post, if if markdown is active you will see the option to switch to the HTML Editor and then the other way around:
I'm just trying to decide what picture I want to put in there.
This is a great article, but this part is somewhat incorrect.
In the case of signal, message content isn't routed over SMS. Only the initial device handshake when you setup the device. The rest is direct to their servers via https and it uses an asymmetric key system on top of the TLS stuff.
When you add a new contact it's just registering their public key in a manner similar to GPG. Signal really is just a glorified GPG client under the hood. Signal's entire customer database is comprised of "phonenumber, publickey" and that's it. We know this because they have been served in the past with a request that amounted to "tell us everything you know about persons, x,y & z".
Message notifications are sent out using push messages, which do route over SMS. But push is a service of the OS provider such as Google, Apple or Blackberry. If these are being held up, alot more than signal is going to fail.
They couldn't be blocked except at the carrier level. The device will fall back to periodic "wakeup" polling if no new notifications are received after a certain length of time. Again this is ajax style polling and occurs over https.
So just to be clear, it's not that you wouldn't get notifications or messages. It's the LEA could get a copy of the little bit of info that says "wake up, you have a message". Thus the most they could deduce is that someone, somewhere sent you a message via signal. They can't get at the message itself since the process of actually checking the message involves something similar to JWT and they would need to eavesdrop the https in order to get the token. Also they wouldn't be able to know who you are talking to without subpoenaing Moxie Marlinspike and pals.
Just wanted to clarify, it's an awesome article though!
Upvoted and resteemed!
That's an article I couldn't write and almost barely understood. Post it! :)
Lol I think I just did. If you want more depth and details upvote this and I'll make it my next topic.
That is right, it's the initial signup where Signal sends an SMS with a code. But, if that SMS is intercepted by a third party, Signal won't know that. Also, during that initial process (correct me if I'm wrong), a key pair is generated, where your public key is stored on their server which it identifies as you, as you explained above. But your description is correct. You are right, I failed to mention that part, but it was well documented elsewhere.
It identifies not as you as the person, but as the phone number (MDN) along with a keypair. There isn't a concept of personages, just MDNs. The MDN is tied to a publickey, and the private key is on the device. Thus if the SMS is redirected, then the initial setup handshake would just fail. But you still need to communicate ownership of the MDN out of band with your contacts.
This is why signal checks your contact list and automatically begins to share public keys. IMHO this is the biggest vulnerability with signal. It should ask you for each contact if you do or do not want to go encrypted with that particular contact and it should allow you to reject. Otherwise anyone who has you in their contact list will know you are on signal. This is more of an OPSEC vulnerability than a real issue though.
One other place where signal looks to be failing is it looks like it is in fact public key per MDN instead of a unique key per contact pair. Dang it, you got me deep diving their code base now :D
Guess I'll make a post and maybe compare signal vs silence.
I gotta say it's really awesome to find out you're still in the hacking/phreaking game. This is a good and surprising read.
Wait till you read my new book, but you better be vigilant. Because our initial run of the book will be to serve KickStarter donors. Once all the rewards are dealt out, a new run would print out more copies of the book. We are formulating the rewards part of the campaign now.
HI there :) so here is a question - but please realize that most of what you wrote went over my head... hahahaa so feel free to dumb down your response as much as you need. I won't be offended! :) but we are all using cell phones, and we are all vulnerable. but if i'm just the average Joe (or Jane lol) what's the likelihood that my phone is being spied on. or.... is everyone's phone basically being spied on by computer programs - and the more trigger words you say - the higher up the "list" your phone number ascends? (sorry for the simple questions ) and i did read the SS7 hack explained: what you can do about it? article that you linked to as well... but i didn't really see what we could do. Unless you're saying - use a program like Whatsapp - instead of normal text messages? Thanks for reading! :)
You're carrying an always on, full featured tracking device complete with GPS, audio, video, accelerometer and signal scanner in your pocket. Seriously, your smartphone would give George Orwell nightmares.
What he's talking about is SS7 hijacking. SS7 is the raw protocol available at the carrier level. NSA has been on that thing like a hooker on a politician since at least the mid 1990s. When I worked for AT&T Wireless Services in the first part of this century, everything he talks about was already in place and regularly used. It's not a rumor, every MDN has been under constant capture since at least 1999. Tracking a missing person by pulling their tower ping history and performing triangulation used to be in my job description.
You've already been "spied upon", numerous times. For example, Verizon will man in the middle your https connections, just to inject a "super cookie" for advertising purposes. AT&T has every bit of data your phone has ever generated going back to PacBell days, possibly earlier, but the longest log I ever saw had a start date of 1996. Don't even get me started on Google and Apple.
What he's talking about is important, but if you've got something to hide, there are bigger security issues than you're worrying about right now. My advice is don't do anything illegal with your phone at all and stay away from "darknets" on it, i.e. don't mess around with Tor, I2P etc. Do that and you'll get lost in the crowd, unless someone is actively seeking you.
Factually speaking, you're already in "the system", but the volume of data being collected is too voluminous for real time analysis. Echelon developed a backlog of 30 mins way back in 2001. I can only imagine that has gotten much worse since the volume of data being collected has increased at a rate "exceeding exponential". At this point our entire intelligence apparatus is mostly just a pork project for Booz Allen Hamilton. Even if you're someone they should be looking at, odds are that most likely they aren't. But you do have records.
Well that was an awesome reply!!!!!! thanks williambanks! No - i'm not doing anything illegal hahaha (but i would almost have to say that, right?) LOL but I'm always just curious about the whole thing. it brings up so many other questions!!! I'm going to have to follow you just to glean bits and pieces from your posts. I have a feeling that it would be way too much info for one conversation. Thanks again for the really great reply! (followed) :) oh... and i upvoted your reply. Don't get excited.... my upvote is currently worth 0.003 cents ;) hehehehe but I still believe in upvoting with my ridiculously puny vote. because it STILL has worth ;) Good day to you! :)
Well - If you use the Anonabox TOR router through your phone, you have nothing to worry about. In one of my Kickstarter rewards, I'm offering a "Blue Anonabox" complete with Whistle thumb drive that blows 2600. Very limited number of these are still available (about 25), so if you jump on this just when the KickStarter program starts, you have a good chance of getting one... it's not only a great Collectable item, it's also practical, and keeps TOR completely off your devices and into a small device you can call a WIFI router.
Yeah so I'm going to be in on it. Make sure to announce it here so we all get a chance to be part of it.
Using WhatsApp is a good start. You can always assume you will be tracked, but are they? Good question, it all depends on how focused the NSA is in targeting you. I've heard stories where innocent people would get mailed a terrorist recruiting site, and its on the NSA target list. So, a 2nd level of intercept might dig up something you said 2 years ago in an innocent context, but 2 years later, could be interpreted as something else, so this innocent person could wind up in the no fly list. But, if that person has been using 'Signal', their conversation would be out of reach of the NSA. Sure, they can track you, even using a dumb phone with no GPS, but they don't know what you're saying, or who you're talking about, if you use Signal. So all of this is a moot point, but when you start using encryption, use it ALL the time.
another question :) when i look at the map of the world... and it shows different countries have higher or lower risks... is that intentional by the country's government? Are they allowing /marketing certain phones in their countries that allow for greater ease of hacking?
To a point, yes. Before cell phones were starting to get popular, getting access to the SS7 network required very expensive telco equipment. So somewhere along the lines, the telcos setup what I call Gateways, using the SIGTRAN layer, where all of the lower layer protocols is just a packet payload as far as the internet is concerned. This significantly reduced the cost for smaller telcos to get in the game. It wouldn't surprise me of some African Native village can have their own Cell tower (OpenBTS), interfaced to an Asterisk box connected via the internet to an SS7 gateway. There was one setup at Burning Man in 2013, and at one of the Defcons of past years setup a "tower". Obviously there is more to it then that, but these would be the major components.
Great posts! Congratulations on making such a splash on Steemit. Hope some of the Steem will help with the funding of your book. So cool to see you here!
Thanx, I'm honored.
Very interesting read, it has always surprised me how hugely popular cellular has become. In the early days everyone understood they were not private and not secure for sensitive information.
Even cordless phone use was done with caution, no one would give out credit card or banking info on such devices. Now it seems everyone just assumes everything is fine lol...
I do not own a smartphone and have no intention to transact business over any network other than my own, but even that is at least as risky as check fraud..
Thanks for sharing this here John!!
No problem!
We can sure that governments will want to maintain some sort of access to the networks to that they can monitor anyone with a phone. I'd hope that at least the telcos can lock down their networks to reduce the chance of rogue elements getting access. No complex system can be completely secure.
You should ALWAYS assume they are listening to you. But your conversation and contacts can stay out of their reach when you use Encrypted apps like signal - By the way, Signal is a real huge "data hog", so if you use it with Cellular data, it can eat up 1.6 gb/hour. My MONTHLY plan is only 2 gb a month. So I use the voice part only when on a WIFI. The Text portion leaves a much smaller Data footprint of course, and unlike the voice part, it is not blocked from China. But I heard Signal has an upgrade (only for Android) that the great firewall of China cannot block. Wickr works from China. At least in the parts where my friend visited.
Yep and the way they did it is pretty awesome...
https://github.com/WhisperSystems/Signal-Android/commit/ae40715526aa0fbad583783be63115bb46b1c2c8
The bandwidth will be an issue for many. I've not had a great need for encrypted communications, but I still find it fascinating
The bandwidth has little effect on the encryption, this is a matter of CPU speed. There might be a slight difference, but as streams are deciphered, CPU is a factor, but once decrypted, the amount of data would almost be the same.
everybody needs encrypted communication. Especially now that Trump is our leader.
He's not our leader in the UK, but I expect we will feel the effects. Of course a lot of our communications goes via the US. I've played with GPG for years, but can't get people to use it. I realise it is complex. We need simple to use solutions
nice
Congratulations @jdcrunchman! You have completed some achievement on Steemit and have been rewarded with new badge(s) :
Click on any badge to view your own Board of Honor on SteemitBoard.
For more information about SteemitBoard, click here
If you no longer want to receive notifications, reply to this comment with the word
STOP