Relief for Jaff Ransomware Victims
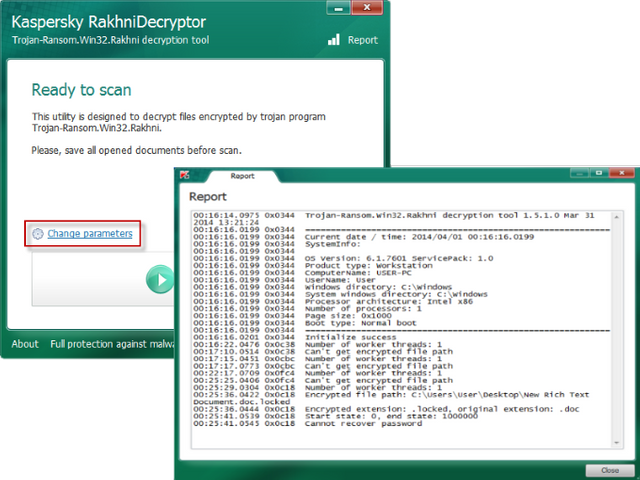
Kaspersky Labs has updated their ransomware decryptor tool to include Jaff ransomware (v1.21.2.1). This is great news for those who have become a victim of Jaff and are wondering if they must pay the hefty ransom (thousands of dollars’ worth of bitcoin). This free tool, from one of the top anti-malware companies, is available at https://support.kaspersky.com/viruses/disinfection/10556
Back in May, the Jaff ransomware was spreading at a rate of 5 million per hour. It is similar to the Locky variant but has a higher ransom. Infection occurs via a malicious email attachment, usually a PDF document, that opens an embedded Microsoft Word file containing a macro script. This macro, if allowed to run, downloads and executes the payload.
Multi-Use Tool
The Rakhni Decryptor can be used to decrypt files that have been altered by the following types of ransomware variants:
- Win32.Rakhni
- Win32.Agent.iih
- Win32.Autoit
- Win32.Aura
- AndroidOS.Pletor
- Win32.Rotor
- Win32.Lamer
- Win32.Cryptokluchen
- Win32.Democry
- Win32.Bitman version 3 and 4
- Win32.Libra
- MSIL.Lobzik
- MSIL.Lortok
- Win32.Chimera
- Win32.CryFile
- Win32.Nemchig
- Win32.Mircop
- Win32.Mor
- Win32.Crusis
- Win32.AecHu
- Win32.Jaff
The detailed instructions are on the site. It is somewhat technical, so take your time and do it right. This may be your only opportunity to recover your files without paying your attackers.
To Avoid the Pain
Prevention is better than a cure. To avoid Jaff and others like it, follow these three steps:
- Don’t open or download files from unknown or untrusted sources. Just don’t do it. You know better.
- Make sure macros are disabled in all your Microsoft Office applications. They are being heavily abused by attackers.
- Install and keep current a trustworthy and comprehensive anti-malware suite from an industry leading security software company. This should include anti-virus, email and web protections, firewall, and even some type of sandbox capability to test files in a safe environment.
- (bonus) Make sure your important files are backed-up regularly and stored off-line. Although not prevention, in the event you find yourself in the middle of a catastrophe, you will be glad your most treasured data is still safe and accessible.
For cures to other ransomware variants, check out the free tools at nomoreransom.org provided by industry leading cybersecurity software companies.
Interested in more? Follow me on LinkedIn, Twitter (@Matt_Rosenquist), Information Security Strategy, and Steemit to hear insights and what is going on in cybersecurity.
Great too see antivirus and cybersecurity companies trying
Advanced system care also had ransomware live protection and had been actively updating their data base to include things such as crybaby. Companies are making progress, hope they can keep it up.
Yes, they are trying to keep pace with all the new ransomware variants as well as working together to provide free recovery tools to victims.
Thank you... I've been running the windows security suite as well as the free Malwarebytes... They probably aren't enough so I'll be running this!
Ransomware is the scourge of computing!
Good information! We don't need regulators, the internet fixes itself exactly like this. Information sharing and reputation systems. Thank you for posting.